Clubhouse Faces New Security Questions After Significant Data Breach
Social Media Today
FEBRUARY 22, 2021
The security of rising audio social app Clubhouse is being questioned after a major data breach was detected over the weekend.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

 data-security
data-security 
Social Media Today
FEBRUARY 22, 2021
The security of rising audio social app Clubhouse is being questioned after a major data breach was detected over the weekend.

BeingOptimist
DECEMBER 6, 2023
Today, we have an exciting journey ahead as we delve into two crucial topics that are at the forefront of our digital era: strong encryption, secure file transfer, and the sensitive nature of data. Confidential document exchange, like legal contracts, medical records or bank details requires maximum security at this level.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Social Media Today
MAY 7, 2020
Multi-participant video streaming app Zoom has acquired secure messaging app Keybase as it continues to refine its data security measures.

Forbes Social Media
MARCH 9, 2023
As pressure mounts on TikTok over concerns that it may be sharing user data with the Chinese government, the company has launched a new data security regime for protecting user information across Europe.

Social Media Today
JUNE 14, 2018
Facebook has added some new requirements for those using Custom Audiences in order to increase the platform's data security measures.

Forbes Social Media
JULY 29, 2019
It could be a very unhappy birthday for users as a security warning over "1000GB of data" message is issued. The WhatsApp messaging service is celebrating its tenth anniversary this year.

Social Media Today
APRIL 9, 2020
Video conferencing platform Zoom has announced the appointment of a new security council, and the addition of Alex Stamos as a security advisor, as it seeks to improve its systems.

Social Media Today
AUGUST 23, 2022
This could be a major blow in Twitter's pending court case against Elon Musk.

Social Media Today
NOVEMBER 16, 2022
TikTok still faces the threat of a full ban in the US.

The Realtime Report
JUNE 12, 2023
PHI draws a high price on the black market and, unlike credit card data theft, can go undetected for years. The most critical consideration for healthcare cybersecurity is the integrity of patient data and the ability to respond quickly to attacks. Cybercriminals scour healthcare networks looking for protected health information (PHI).

The Realtime Report
MARCH 28, 2024
Drones can monitor and assess crop yields far more quickly than human workers and can provide key data that determines the ongoing actions of farmers. API Gateways For Secure Online Applications It is now estimated that approximately 94% of all enterprises use cloud-based IT systems.
BeingOptimist
JANUARY 21, 2024
If you aren’t sure what that is, VPN is the service responsible for creating a secure and encrypted connection between a device and a network. The significant key components are a VPN Client, VPN Server, Encryption Protocols, Authentication and a Secure Tunnel. Send to VPN Server: Your hidden data is sent safely to a VPN server.

Forbes Social Media
FEBRUARY 18, 2020
Gaining greater insight into these queries will help organizations take the appropriate next steps and avoid the dreaded civil action and financial penalties.

Social Media Today
SEPTEMBER 27, 2022
TikTok is working with US officials to provide more transparency over its data processes and algorithms.

Social Media Today
MARCH 22, 2019
Facebook has found that millions of user passwords were being accessed internally via a plain text document without adequate protection.
Convince & Convert
FEBRUARY 21, 2024
Consider that if you have executives with public facing written, spoken, or video content that anyone could utilize that data to replicate their voice and make trouble. Data Security Challenges Most leaders probably don’t want their finance team feeding profit and loss data into ChatGPT to save 5 minutes of their time analyzing some data.
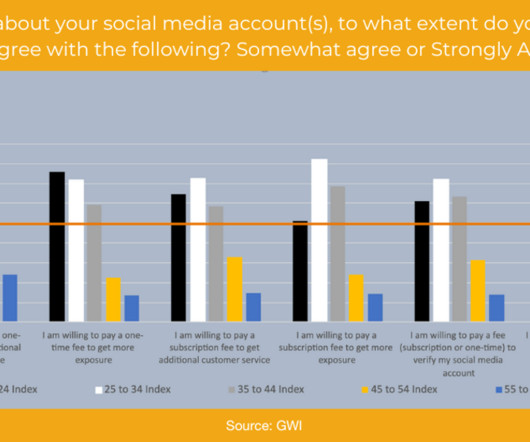
Ignite Social Media
JUNE 23, 2023
New data shows opinions vary widely by age. New data has shown that a substantial number of users are open to paying for social media accounts in exchange for extra privacy, security, and other benefits, with younger people being much more willing to consider paying than those over age 45. According to the data, 48.9%

Forbes Social Media
OCTOBER 9, 2019
Twitter has apologised for allowing advertisers to target ads using the email addresses and phone numbers provided by users for account security.

Social Media Today
OCTOBER 3, 2019
Google has announced a new set of security features, including a password check-up tool, capacity to auto-delete your usage history and more.
BeingOptimist
JANUARY 29, 2024
We will talk about how Portugal VPNs can be used for extra security. To understand how secure VPNs are , you need to understand what a VPN does for you. VPN is often used because, in some countries, a lot of data is restricted. To retrieve search data and still stay anonymous VPN is being used.
The Realtime Report
OCTOBER 16, 2023
A centralized list of vulnerabilities with standardized names makes it easier for security professionals to track threats and take action. It includes losing data and intellectual property and disseminating false or misleading content to influence beliefs and behaviors. Identify and patch them to protect your systems.

Sprout Social
FEBRUARY 29, 2024
This article will explore the diverse roles AI plays in enhancing business functions like marketing, operations, product development, human resources, customer support and security. Machine learning (ML) Machine learning algorithms analyze data, identify patterns and make predictions based on their results.
The Realtime Report
APRIL 1, 2024
Address Security Concerns Like any internet-based service, SIP trunking raises security concerns such as unauthorized access, eavesdropping, and denial-of-service (DoS) attacks. It is crucial to use security measures, such as encryption, firewalls, and access controls, to protect sensitive information and ensure privacy.

The Realtime Report
NOVEMBER 23, 2020
Over the last year, SMEs decreased their IT security by an average of $4.9m! 32% of businesses see ‘no reason to invest so much in IT security’ Even though there has been a drop in security investments, 66% of SMEs say it is worth making ‘huge’ investments in cybersecurity practices. Kaspersky Report Data.

The Realtime Report
SEPTEMBER 21, 2021
Facebook has had its fair share of security mishaps over the years, and 2021 is no exception. According to the data analyzed by the Atlas VPN team, average monthly searches for the keyword ‘Facebook account hacked’ have grown by a whopping 93% since last year.

The Realtime Report
OCTOBER 13, 2022
Encryption is a process of transforming readable data into an unreadable format. This is done using an algorithm, a set of rules that can be applied to the data to change it. The purpose of secure encryption is to protect information from being accessed by unauthorized people. About Encrypting. Types of Encryption.

The Realtime Report
JANUARY 9, 2023
How To Overcome The Challenges Of Managing Enterprise Data. Managing your enterprise’s data can be challenging but possible. With the sheer volume of data, it can be difficult to know where to start and how to stay organized through the process. Develop A Data Management Strategy.
Sprout Social
JANUARY 19, 2023
There isn’t much regulation at the moment, which has led to inconsistent expectations and user experiences, especially surrounding security and privacy best practices. According to a Sprout survey of 300 marketers responsible for their brands social media strategy, 64% cite data, privacy and brand safety as concerns within the metaverse.

Social Media Today
MARCH 25, 2022
After reports that Meta may be forced to leave the EU, a new agreement in principle has been reached to secure transatlantic data flows.

Tweaklibrary
JANUARY 25, 2022
iPhone has the best security features when compared with other OS in the world but despite the high level of security provided in the iPhone, there are some loopholes by which your data can be at stake. These are some minor-looking, major loopholes by which your data can be compromised. Password & Security.

Oktopost
DECEMBER 19, 2022
In this article, we’ll discuss the most common social media security risks, along with best practices to protect your social media accounts from hackers. Quick Links: 6 Common Social Media Security Risks. Secure Your Login Information. Use a Secure or Private Wi-Fi Network. Secure Your Business Hardware.

BeingOptimist
FEBRUARY 6, 2024
These are virtual private networks that allow you to connect your device to a wider server so that you can extract formation and at the same time do that in a secure way. These VPNs use encryption protocols to secure the data that you will transmit between your device and the VPN server. How To Choose a VPN?

The Realtime Report
JULY 7, 2020
Secure Your Physical Premises. If your business has a physical property, whether a brick and mortar store, or whether you have an office or warehousing facilities, then these will need to be secured in the best possible way. You should think about: Secure locks on all doors and windows. Secure fire exits.
The Realtime Report
DECEMBER 5, 2022
Using a secure VPN is not just about bypassing Internet restrictions; online privacy is another major issue. Your online activity and data are exposed to anyone who has access to the Internet unless you hide your tracks as a cleaner would. Even your ISP (Internet Service Provider) spies on you and might log your data.

Social Media Today
JULY 16, 2021
LinkedIn has repeatedly said that claimed data 'hacks' are not a result of security flaws.

Sprout Social
DECEMBER 6, 2023
But it can be a challenge for the marketing teams on the digital front lines to overcome the concerns of security and privacy teams—especially at the intersection of HIPAA and social media.” In your training, highlight proper usage of customer data on social media and common HIPAA violations. Looking for more resources?

BeingOptimist
DECEMBER 6, 2023
Unlike on-premise servers or traditional data centers, Azure billing is based on resource consumption, not reserved capacity. In the Central US region, hot locally redundant block blob storage (LRS-HOT) starts at $0.0184 per GB with three copies in one data center. This approach helps reduce costs and improve application security.

Oktopost
FEBRUARY 12, 2024
Regulatory bodies, such as FINRA, place rules on language usage, terms, and the archiving of data, which is no different for social. Oktopost allows you to easily capture and securely store your social media posts. These fines can range from thousands to millions of dollars – potentially crippling a financial institution.

Ignite Social Media
MARCH 2, 2021
People have become increasingly concerned about the security of their mobile devices. Security issues plague some of the most popular social media platforms. Near the end of 2020, a Chinese startup leaked 400 GB of scraped data from Facebook, Instagram and LinkedIn. Like Signal, MeWe dedicates itself to privacy and security.

BeingOptimist
AUGUST 29, 2023
The activity falls under different federal and state laws pertaining to privacy, information security, data protection, and employment rights. Cyber background checks are crucial for organizations to ensure the security and integrity of their infrastructure and data.

BeingOptimist
APRIL 26, 2023
As internet connectivity has become mandatory for daily communication, work, and entertainment, your online security has become a priority for many people. An undeniably excellent way of securing your online activity is by using Virtual Private Networks (VPNs), such as iTop VPN. This VPN promises unrivaled online privacy for its users.

BeingOptimist
JUNE 20, 2023
When you upgrade to a new iPhone, one of the most important tasks is to transfer data to new iPhone. However, with the right tools and methods, you can easily clone your iPhone and transfer all your data effortlessly. Data Security: By cloning your iPhone, you can ensure that your sensitive data remains secure.
Sprout Social
AUGUST 21, 2023
In this article we’ll define what AI ethics are, why brands should be concerned and the top ethical issues facing marketers, including job security, misinformation and algorithmic bias. Impact on jobs and job displacement Robots securing world domination is the least of our worries—at least for now. What are AI ethics?
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?

Let's personalize your content